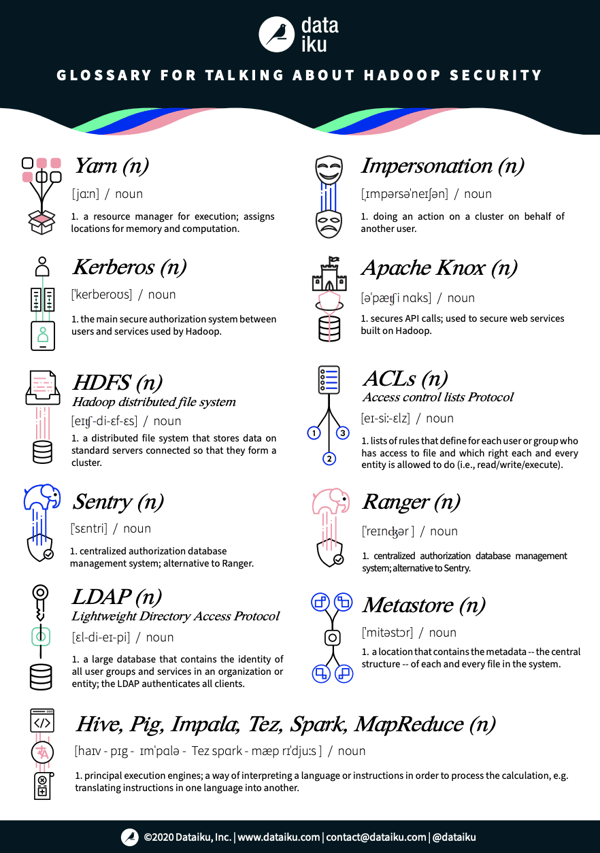
Between growing data and analytics teams, more collaborative projects, and GDPR, security and governance are becoming bigger issues. As organizations' analytical maturity improves, it's increasingly critical that business and technical users alike understand data best practices.

Who is allowed to use what data? And what are they allowed to do with it? Big data brings Hadoop clusters, which use Kerberos and ACLs and LDAPs, all to manage rules and access rights. But what are those exactly, and how do they work?
When working in data and analytics, communicating with IT professionals who use technical vocabulary is commonplace. What is a yarn, and what is a metastore? What is the difference between Sentry and Ranger? (Hint: not much.) What does Apache Knox do? What do we mean by impersonation? And what do Hive, Pig, Impala, Tez, Spark, and MapReduce all have in common?
We've created a glossary with some key terms to think about when discussing Hadoop security.